Synapse – SQL Admin
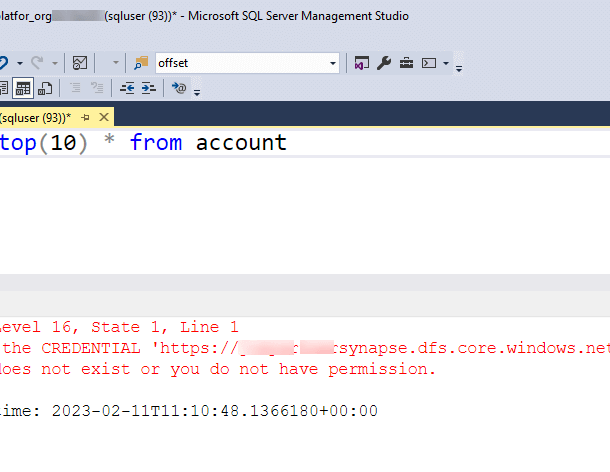
It looks like the rights of the SQL Admin user in the database created by Synapse Link for Database have recently been changed. Prior to 2023, the SQL Admin user account has able to query all the external tables created by Synapse Link for Dataverse. Now if you query a Dataverse external table using the SQL Admin account you will get an error “Cannot find the CREDENTIAL [] because it does not exist or you do not have permission.” This error indicates that the account does not have access to the underlying storage.
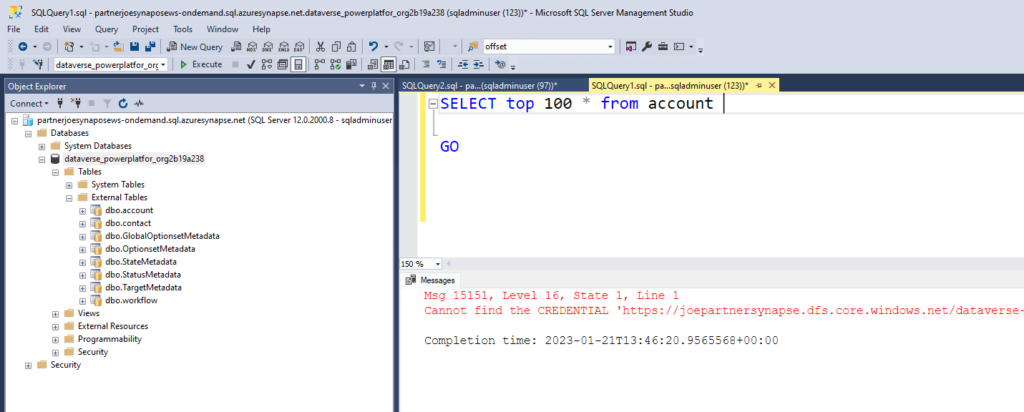
Having previously installed Synapse Link for Dataverse on numerous occasions I was a bit perplexed. It took me a while to figure out the difference. By running the following query in the master database of my existing Synapse Link for Dataverse environments I discovered they contained a credential record that provided access to the storage account.
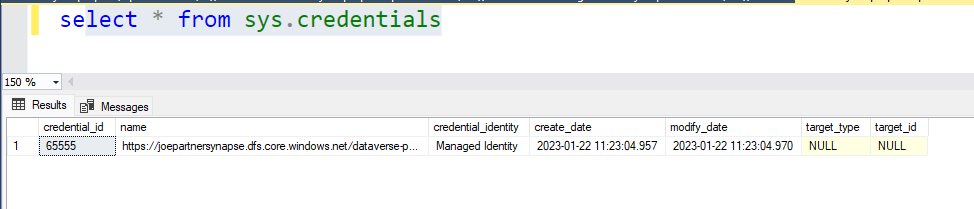
To give the SQL Admin user access to the storage I created a credential for the Managed Identity of the Synapse service. The url comprises of the storage account’s Data Lake Storage endpoint and the container for the Dataverse environment.
CREATE CREDENTIAL [https://joepartnersynapse.dfs.core.windows.net/dataverse-powerplatfor-org2b19a248]
WITH IDENTITY = 'Managed Identity';The SQL Admin account is a SQL user and so it cannot be given permissions to the storage account using Azure Active Directory. With the credentials in place when the SQL Admin user runs a query the Managed Identity delegates permissions to the underlying storage.
I have not noticed anybody reporting this issue. I have seen it in two different tendencies so I am assuming this is a platform change and not just me! It could well be that not many people use the SQL Admin account and this is highly likely as Azure Active Directory is the preferred authentication method for Synapse. I have covered this in another post.